Sometimes, devices don’t work as smoothly as they should. In these and other cases, a factory…
Continue ReadingV.P.N
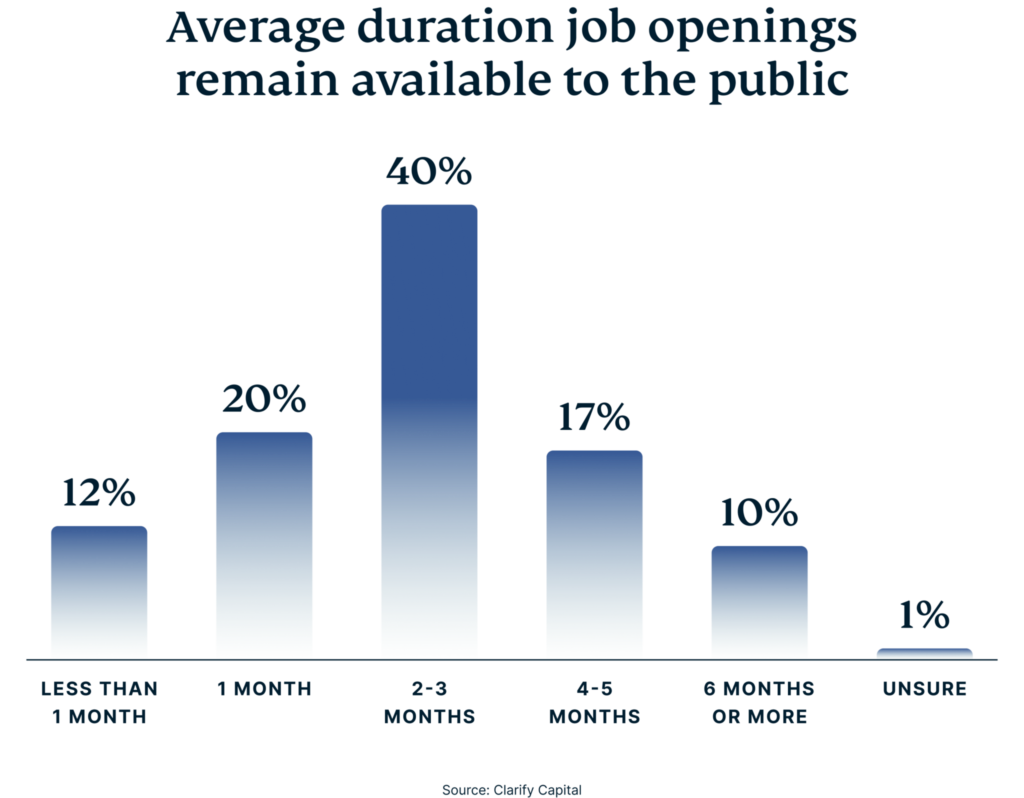
Ghost Jobs: Tips to Avoid Fake Job Posts
Ghost jobs, which are job postings for roles that are not actively being hired for, can…
Continue Reading
US Age Verification Laws: Analyzing the Spread and Impact
Since 2022, many states have passed laws requiring adult websites and services to verify their users’…
Continue Reading
What is quantum computing? Everything you need to know
In modern technology, where innovation is ceaseless and boundaries are constantly pushed, the emergence of quantum…
Continue Reading
How to Recover Hacked Telegram Account
Telegram is known for being one of the most secure instant messaging apps around. But what…
Continue Reading
Is WWW2 Safe? An Intro to Subdomains
If you’ve seen one website domain, it doesn’t mean you’ve seen them all. One of the…
Continue Reading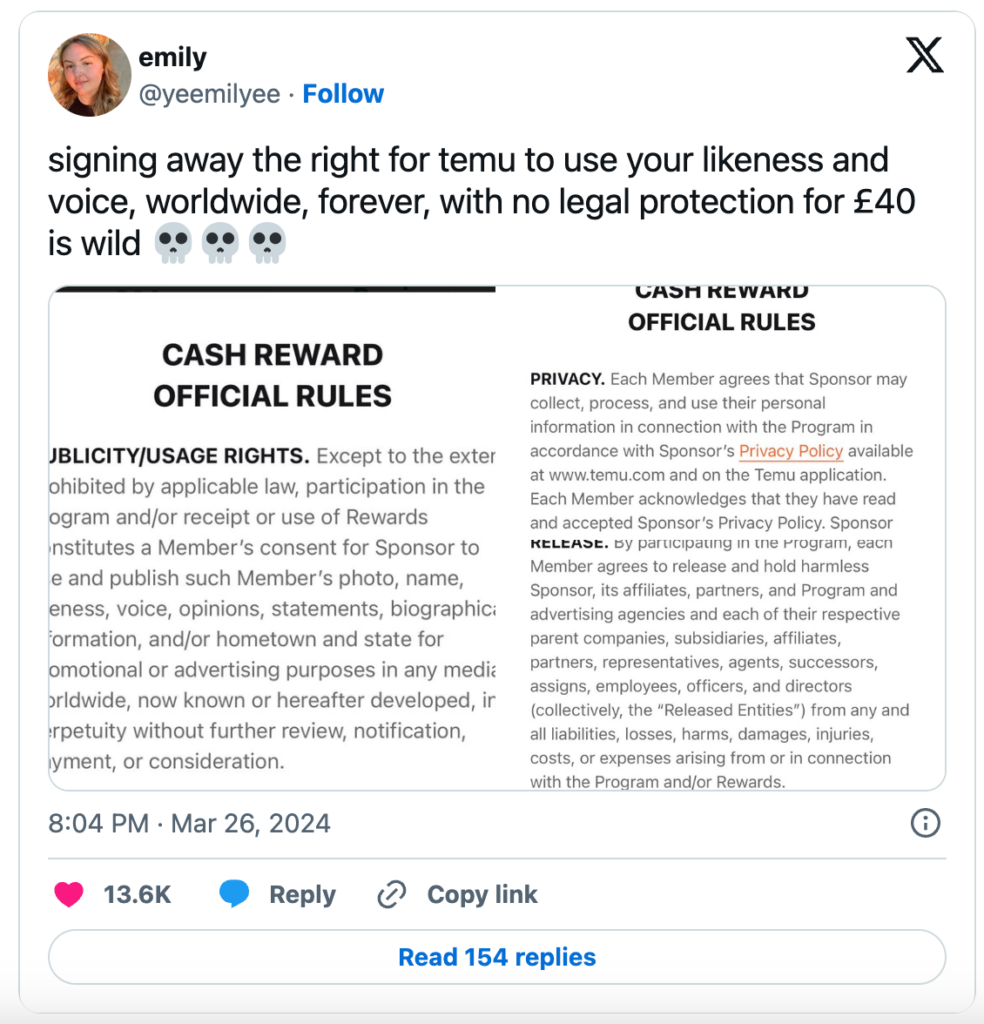
Cash for Sign-Ups: It’s Your Data for Sale
Temu, a Chinese e-commerce platform with global popularity, recently offered cash incentives for new user registrations,…
Continue Reading
How to Tell Your Router Is Hacked
Your Wi-Fi router is an important part of your home, keeping your devices like laptops, phones,…
Continue Reading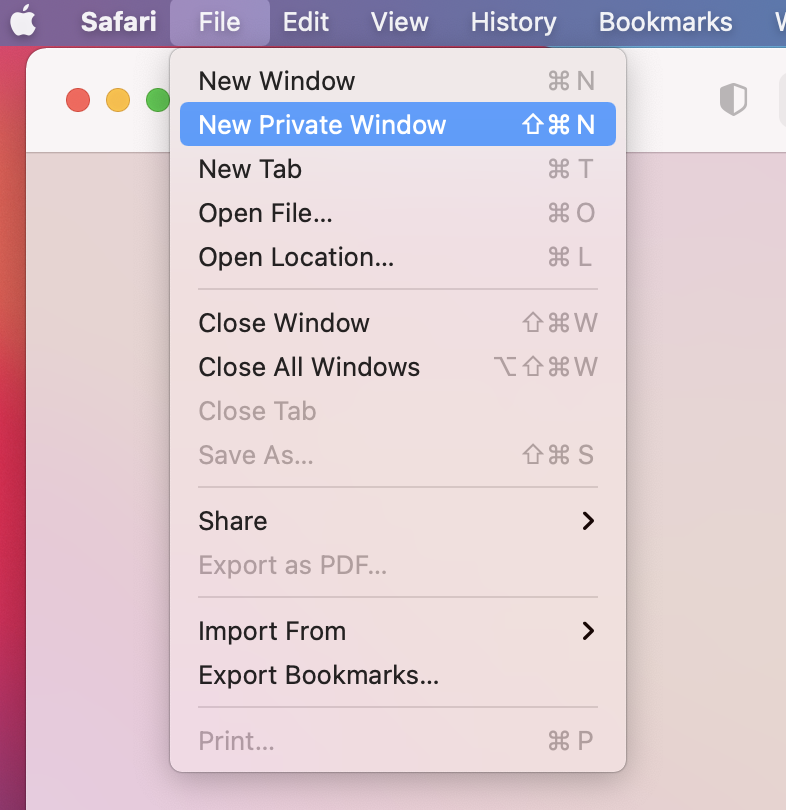
What Is Incognito Mode, and Is It Safe?
You’re probably already familiar with the concept: You can open a new private, or ”Incognito,” window…
Continue Reading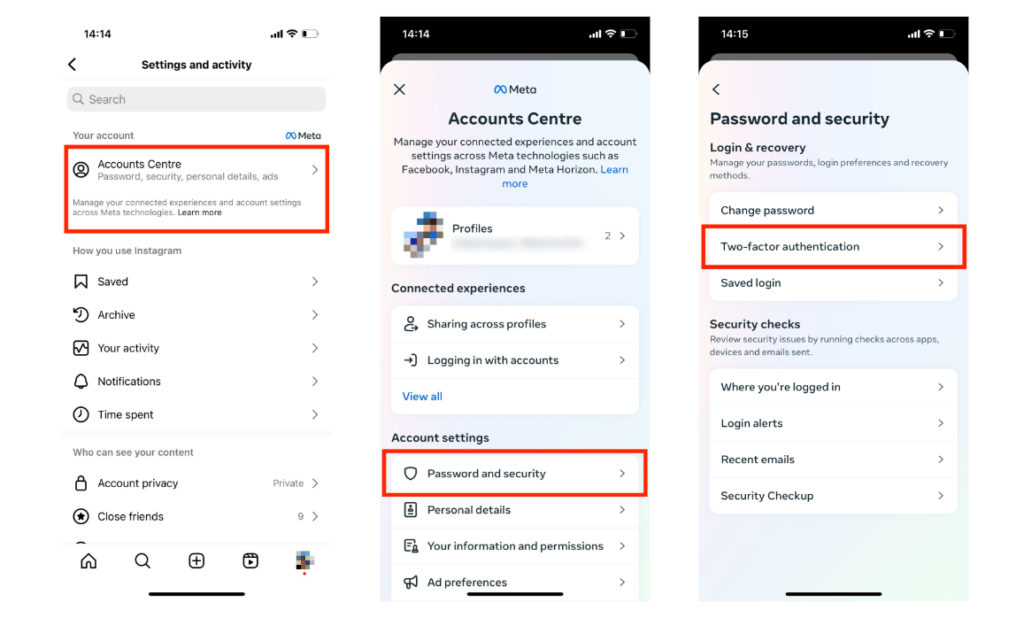
Instagram Phishing: Protect Your Account
While Instagram can offer a platform for connection and creativity, it can also be a hunting…
Continue Reading