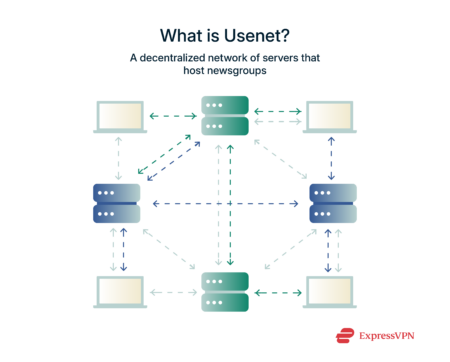
Long before TikTok trends, Instagram scrolls, and YouTube rabbit holes, the internet was a much quieter…
Continue ReadingV.P.N
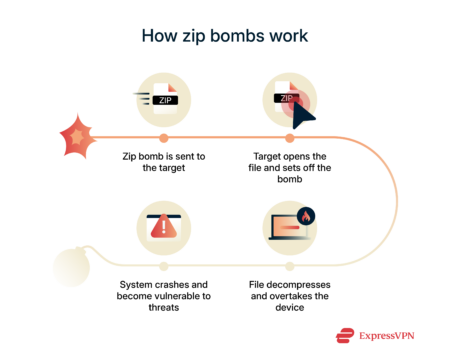
What is a zip bomb, and how it affects devices
Zip bombs may look like tiny, harmless files, but they pose a real threat. Imagine receiving…
Continue Reading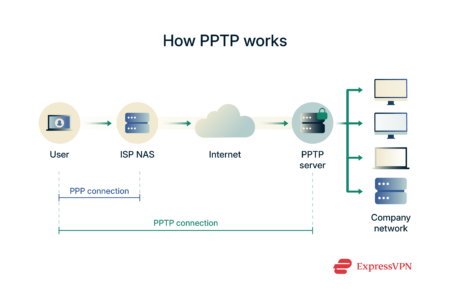
Discover PPTP (Point-to-Point Tunneling) VPN protocol
Point-to-Point Tunneling Protocol (PPTP) is one of the oldest VPN protocols still in use today. However,…
Continue Reading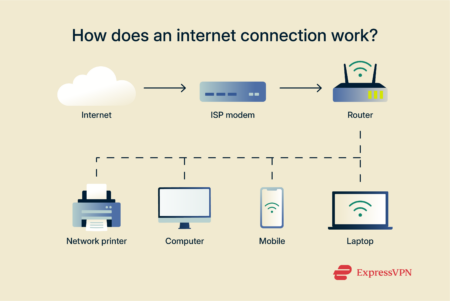
Types of internet connections | ExpressVPN
Some people think “Wi-Fi” is the internet—but that’s a common mix-up. Wi-Fi is just the way…
Continue Reading
What is my DNS? Find and check your DNS instantly
When you want to access a website or online platform, you type the address into your…
Continue Reading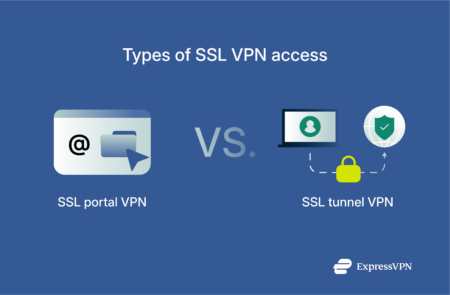
What is SSL VPN and how it works
SSL VPN (Secure Sockets Layer Virtual Private Network) is a tool many organizations rely on to…
Continue Reading
IPVanish Partners with URC to Promote Cybersecurity
IPVanish Partners with URC to Promote Cybersecurity | IPVanish …
Continue Reading
Brute force attack: What it is and how to prevent it
A brute force attack is exactly what it sounds like: instead of looking for a secret…
Continue Reading
Is Bitly safe? Check short links before you click
Shortened URLs are everywhere—on social media, in text messages, and across the web. Services like Bitly…
Continue Reading
Phishing Scams Exposed: How to Stay One Step Ahead
Phishing Scams Exposed: How to Stay One Step Ahead | IPVanish…
Continue Reading