Academic research contributes greatly to developments surrounding online privacy and cybersecurity, at times influencing the design…
Continue ReadingV.P.N

Wi-Fi pineapple attacks: what they are and how to avoid them
Fruit and cybersecurity terminology don’t usually blend. But at least one notable exception exists in the…
Continue Reading
How to Permanently Delete Kik Account in 2023
Kik, a chat app, has been associated with a barrage of news items concerning predators communicating…
Continue Reading
Introducing the IPVanish VPN Kill Switch app for Fire TV
This post examines how the VPN Kill Switch app enhances your Fire TV with improved online…
Continue Reading
ExpressVPN at Hackathons and CTF Competitions
Capture the Flag competitions (or CTFs for short) are the exhilarating battlegrounds where talented cybersecurity experts…
Continue Reading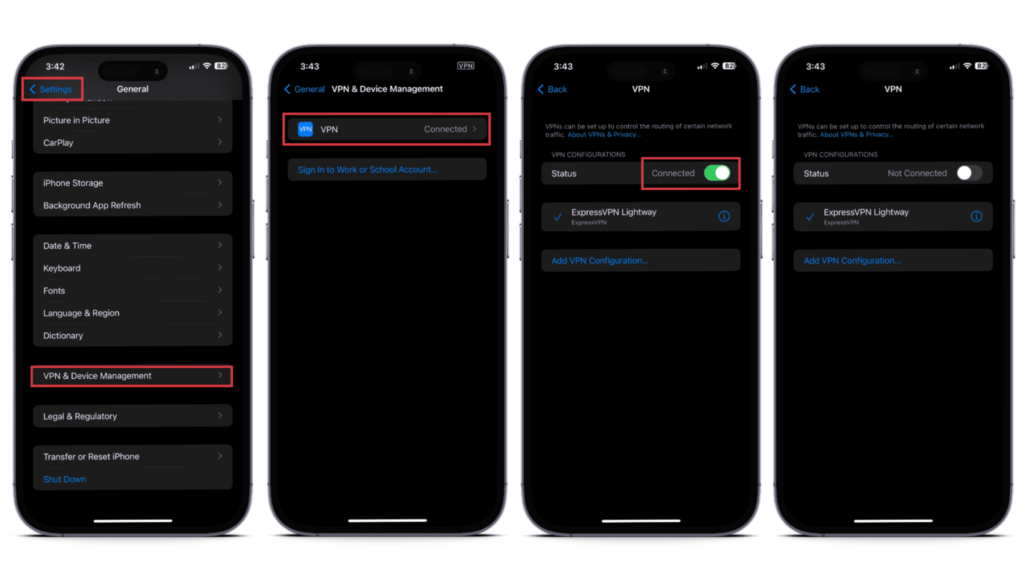
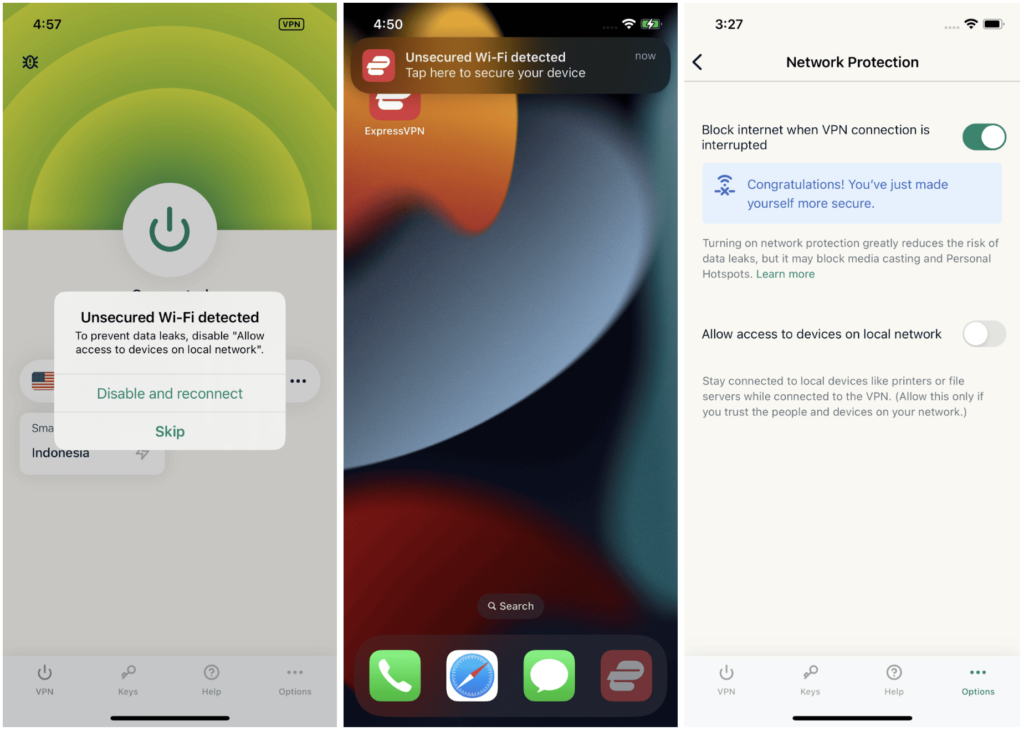
How to Turn Off VPN on Your iPhone (2 Ways)
A VPN gives you greater online privacy and security, so it’s a good idea to keep…
Continue Reading
What you need to know about a VPN tunnel
You might know what a VPN is used for, but what is it really? A virtual…
Continue Reading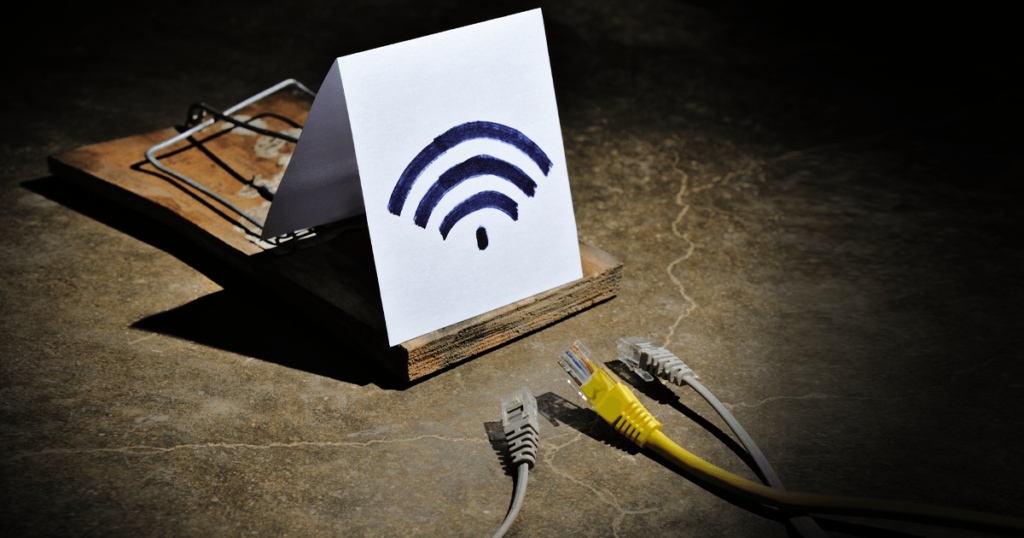
Rogue access points: what they are and how to combat them
There are many ways that modern hackers can attack a device. Some of the most common…
Continue Reading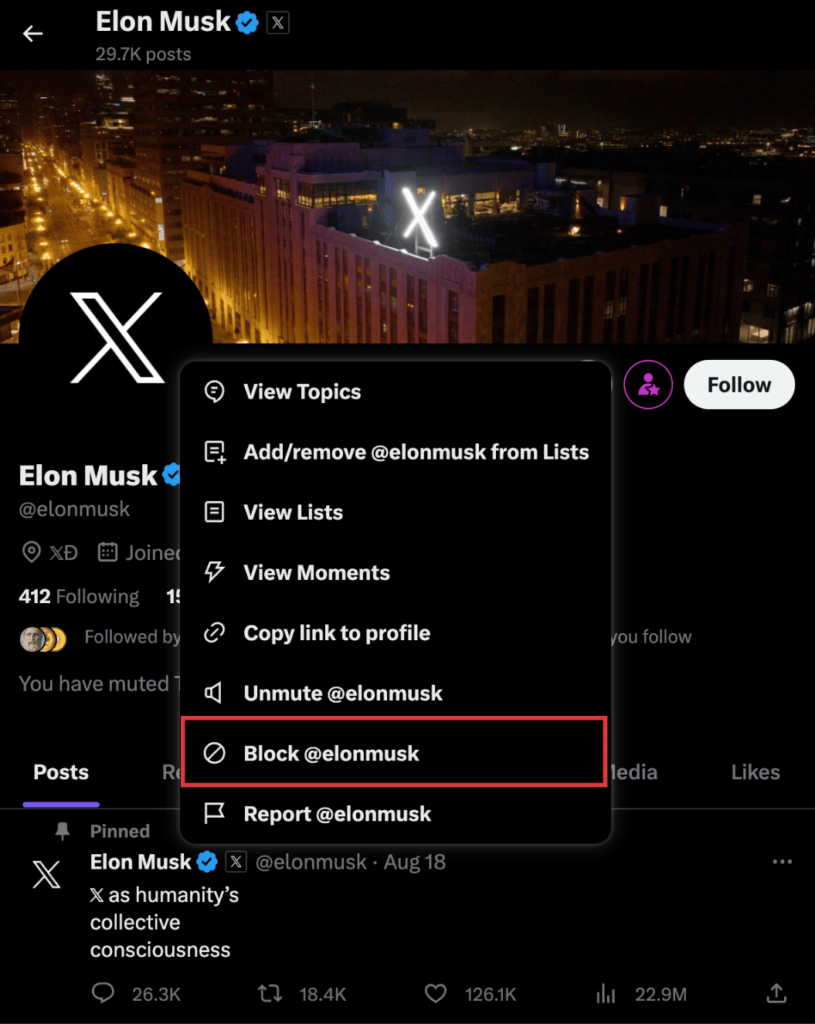
X (Twitter) Wants to Stop You Blocking Users
Elon Musk’s unyielding drive to revamp Twitter, now known as X, continues with yet another major…
Continue Reading
What Are Pig Butchering Scams?
Pig butchering scams are a type of investment fraud that involves tricking targets into investing in…
Continue Reading